Audit Types & Filtering
Knowing who has done what in your application is critical for multiple reasons, including security, compliance, debugging and even just plain old monitoring. Audit Logs are a great way to track who did what, when they did it, and why they were, or were not granted the permissions.
They are a useful tool both for you and your team as the maintainers of your application, but also your end-users, who want to track their own usage and actions within the app.
Automatic Log Generation
As Permit.io powers your application, you are getting automatic audit logs.
Enforcement points, along with resource and action definitions, and user/tenant configurations automatically come together to generate the full picture needed for an audit log entry.
You'll find that the Permit web interface hosts a specialized page where you can conveniently view your audit logs. Alternatively, access them
directly in your deployed PDP microservice. With logs being written to stdout/stderr, it's easy to directly integrate them with your
preferred logging platform.
Types of Audit Logs
There are two types of audit logs:
- Basic audit logs - these are the basic logs reflecting actions in regards to your policy rules.
- Decision logs - more in-depth logs reflecting "why" the policy engine made a decision.
Viewing your Audit Logs
Navigate to the Audit Log page in the Permit dashboard.
We periodically delete old audit logs to maintain system efficiency. If you need access to older logs or would like to extend log retention periods for your account, please reach out to us via Slack or email us at help@permit.io.
Filtering
You can filter audit logs based on user, date, decision & tenant.
Max number of results for this api is 10,000 To obtain additional results readjust the query's time window, or apply additional filters
Decision Logs
Every time a permission check takes place, not only are we logging the details of who initiated a particular action on a resource and whether it was approved or denied, but we also provide a detailed decision log. A decision log represents the real-time status of the ongoing decision, sourced directly from the OPA (Open Policy Agent) engine and presented in a user-friendly format by our system.
Furthermore, we take an extra step to analyze each decision log closely to furnish you with a comprehensive, human-readable explanation that delineates the underlying reasons behind the outcome. This effort is designed to facilitate a seamless understanding of why a particular permission was granted or denied, enhancing transparency and efficiency.
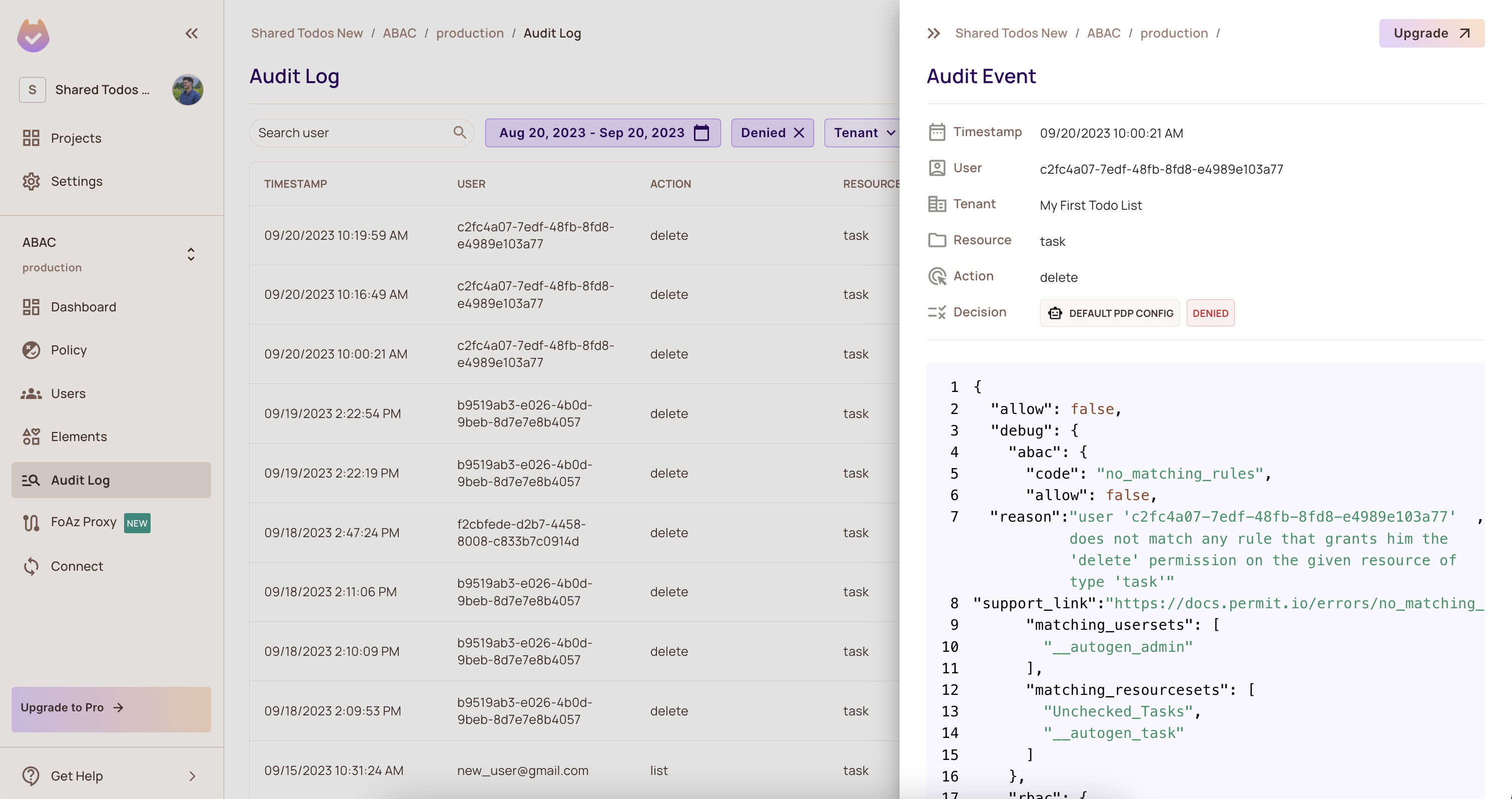
Below, you can find an example of what a human-readable reason looks like inside of each decision log.
"reason": "user 'c2fc4a07-7edf-48fb-8fd8-e4989e103a77' does not match any
rule that grants him the 'delete' permission on the given
resource of type 'task'"